5 Steps to Build a Penetration Testing RFP That Gets Better Proposals
A vague RFP gets vague proposals. Five concrete steps to write a penetration testing RFP that pulls in accurate, comparable bids — without the scope ambiguity that pads pricing.
A vague RFP gets vague proposals. If your penetration testing request for proposal lacks detail on scope, compliance, or deliverables, the responses you receive will be padded with assumptions and generic pricing. This guide walks procurement teams, IT leaders, and security professionals through 5 concrete steps to write an RFP that gives pentest companies what they need to submit accurate, comparable proposals. The result is less back-and-forth, sharper pricing, and a clearer basis for evaluation.
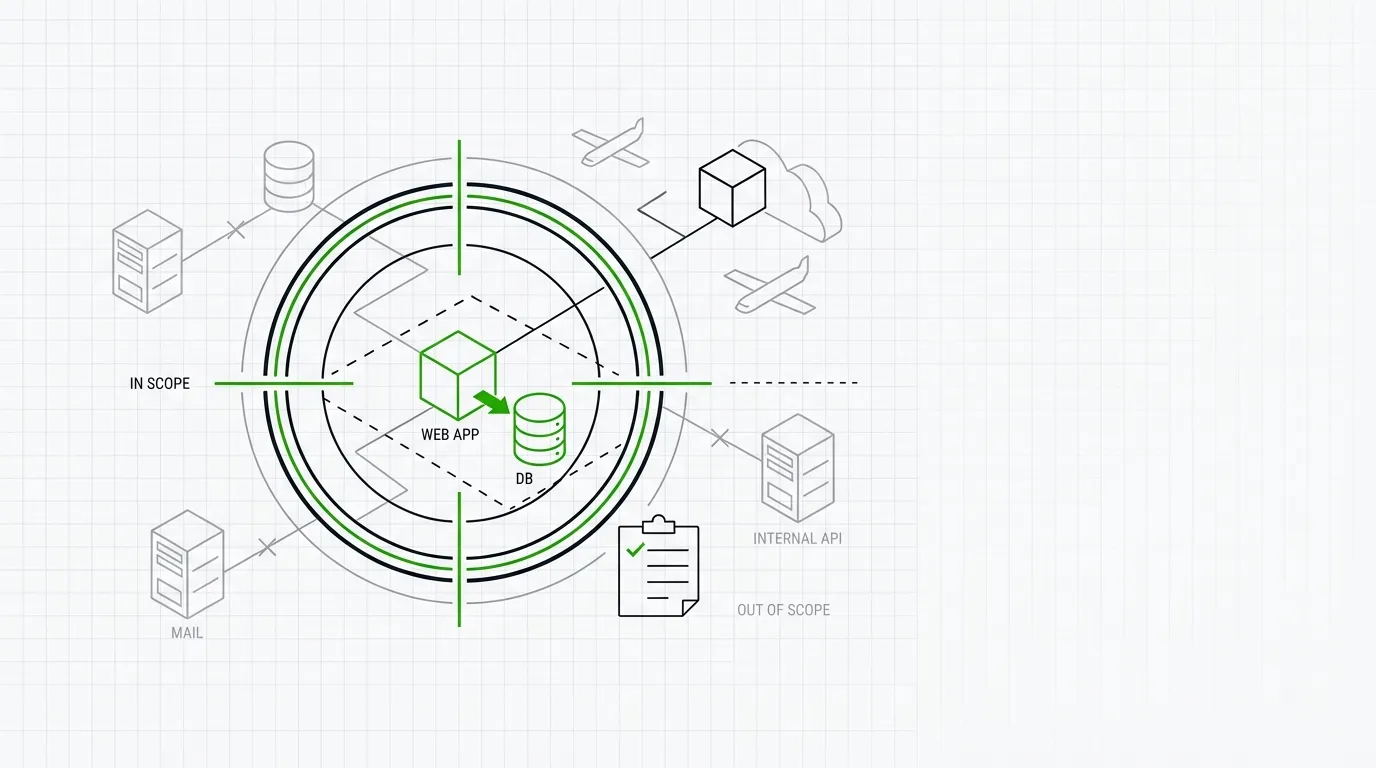
1. Define scope with enough detail to price accurately
Ambiguous scope is the single biggest reason pentest proposals vary wildly in cost and coverage.
Specify exactly what is in scope: the number of external IPs, internal network segments, web applications, APIs, mobile apps, and cloud environments. State whether you need black-box, grey-box, or white-box testing. Include the number of user roles for authenticated testing and whether production or staging environments will be used. For example, an RFP that says “test our web application” will get estimates ranging from $5,000 to $80,000. An RFP that says “authenticated grey-box test of a single web application with 4 user roles, 47 API endpoints, hosted on AWS” gives companies enough to price the work precisely.
2. List compliance and regulatory requirements upfront
Pentest companies need to know which standards and frameworks your assessment must satisfy before they scope the engagement.
State every compliance requirement the engagement must address. This includes PCI DSS, SOC 2, HIPAA, ISO 27001, DORA, or any sector-specific regulation. If you need the final report mapped to a specific framework or formatted for an auditor, say so in the RFP. Different standards impose different testing methodologies, reporting structures, and evidence requirements. A company quoting against PCI DSS 4.0 requirements will scope differently than one quoting a general network pentest. Stating these requirements upfront ensures proposals are aligned to your actual needs.
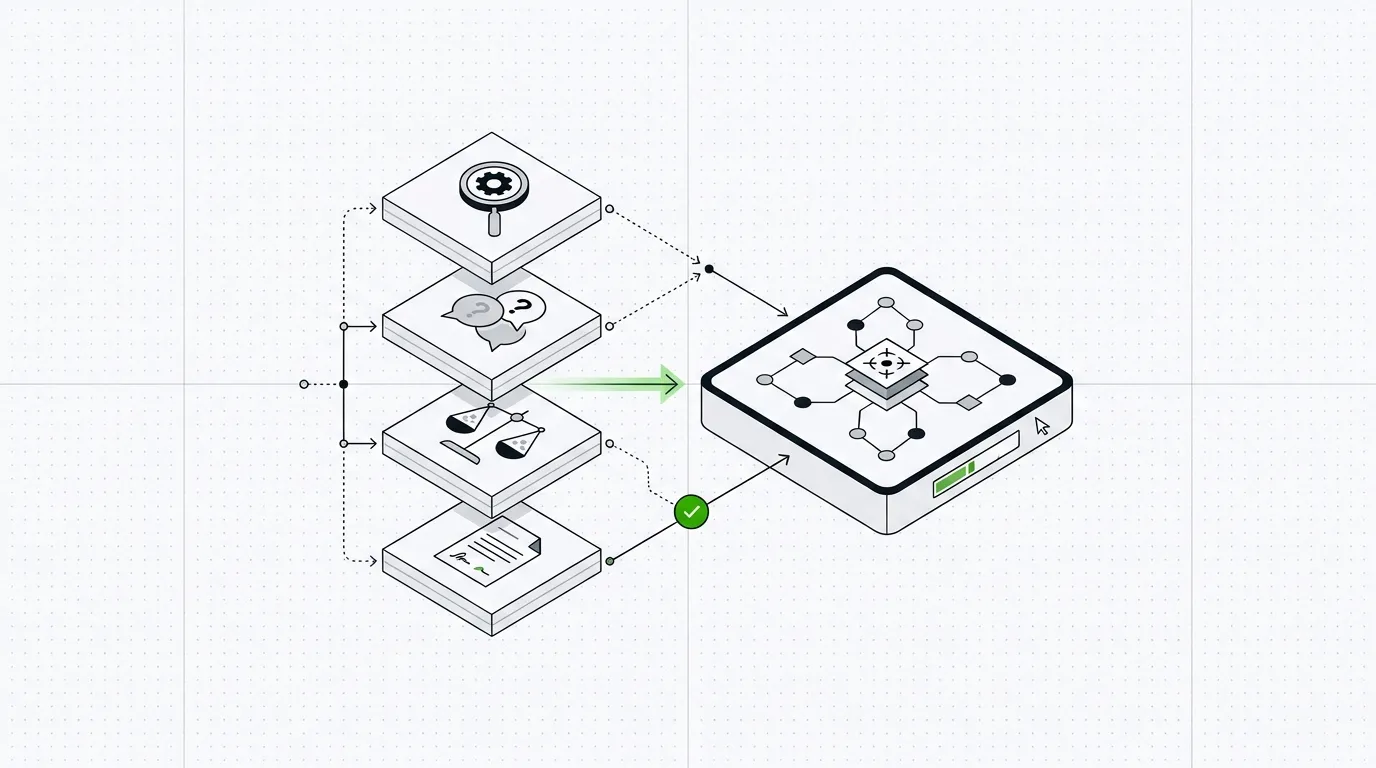
3. Set evaluation criteria and share the weighting
Telling respondents how you will evaluate proposals removes guesswork and improves the quality of every submission.
List your evaluation criteria in the RFP and assign each a weight. Common criteria include relevant industry experience, team certifications (OSCP, CREST CRT, GPEN), methodology (OWASP, PTES, NIST SP 800-115), past performance with similar environments, price, and timeline. If you weight certifications at 20% and price at 30%, say so. Companies will tailor their proposals accordingly, and your comparison across submissions becomes straightforward. Without published criteria, you get proposals optimized for different things, making apples-to-apples comparison difficult. You can search pentest.fyi by certifications and services to identify companies that match your criteria before the RFP goes out.
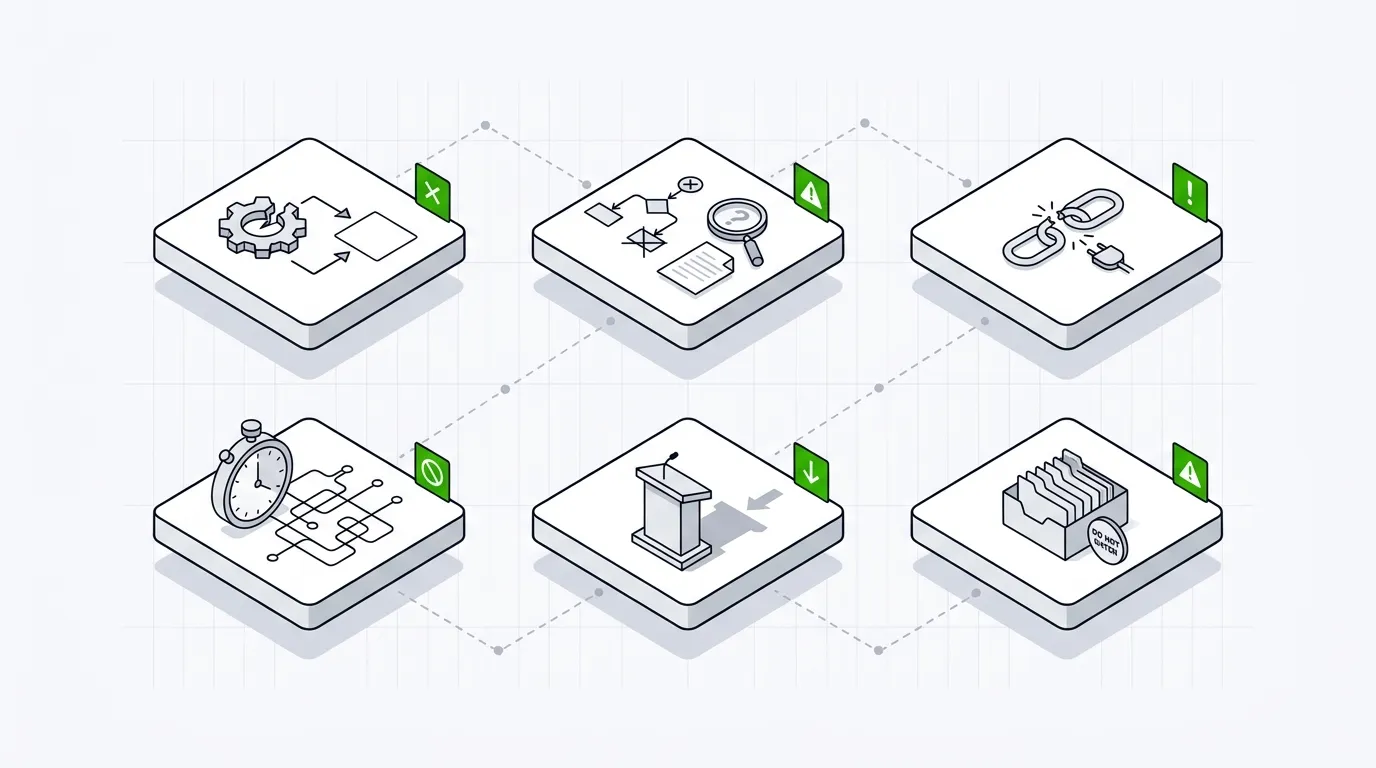
4. Require a sample report and remediation guidance
Asking for a sample deliverable lets you assess report quality before you commit to an engagement.
Request a redacted sample penetration test report as part of the proposal. This is the single most useful artifact for evaluating a company’s work product. Review it for clarity of findings, severity ratings (CVSS or equivalent), reproducible proof-of-concept steps, and actionable remediation guidance. A good report should be usable by both your security team and your developers without additional translation. Also ask whether the company provides a retest period and at what cost. If two proposals are close on price, the sample report will often make the decision obvious.
5. Specify communication and project management expectations
Setting clear rules for communication during the engagement prevents surprises and ensures critical findings reach you fast.
Define how and when the testing company should communicate with your team. State your requirements for critical vulnerability notification (e.g., within 2 hours of discovery via a secure channel), daily or weekly status updates, and a final debrief meeting. Specify who the primary point of contact is on your side and what access or credentials will be provided at kickoff. If you need testing restricted to specific hours or maintenance windows, include that. These details affect staffing and scheduling on the company’s side, which affects pricing. Spelling them out in the RFP ensures proposals reflect the actual engagement, not a best-case assumption.
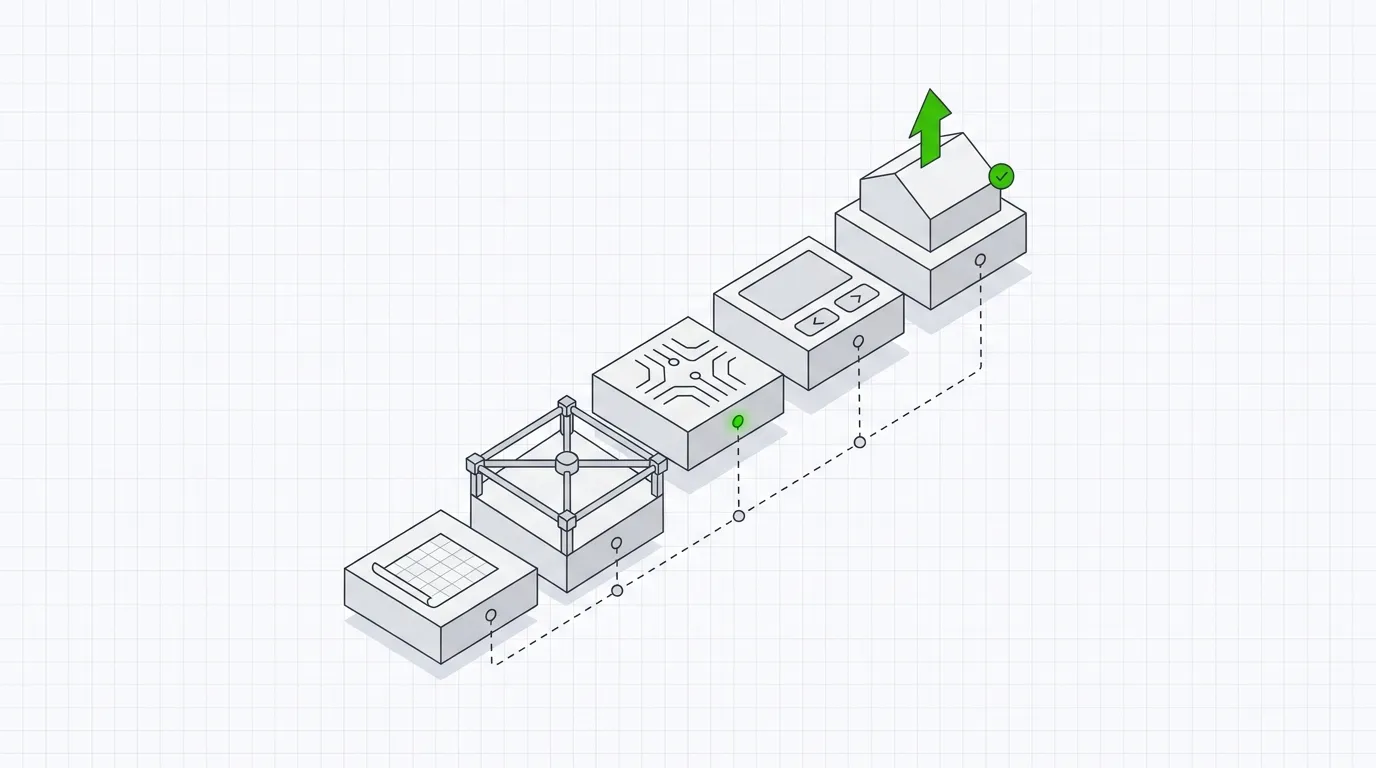
A well-structured RFP saves time for both sides. It reduces follow-up questions, produces comparable proposals, and shortens your evaluation cycle. Use these 5 steps as a checklist the next time you draft a penetration testing request for proposal. If you need to identify companies that match your scope, certifications, or location requirements before sending the RFP, search the directory at pentest.fyi. We list 7,759 companies across 104 locations, filterable by service, certification, and region.
Frequently Asked Questions (FAQ)
How long should a penetration testing RFP be?
Most effective pentest RFPs are 3 to 6 pages. Focus on scope, requirements, and evaluation criteria. Unnecessary background about your organization adds length without improving proposal quality.
How many companies should I send my pentest RFP to?
Three to five companies is a practical number. Fewer than three limits comparison. More than five increases your evaluation workload without proportionally improving outcomes. You can search pentest.fyi by location, service, and certification to build a shortlist.
Should I include a budget range in the RFP?
Including a budget range is optional but often helpful. It signals that you have realistic expectations and helps companies right-size their proposals. If you omit it, expect wider variance in pricing across submissions.
What is a reasonable response timeline for a pentest RFP?
Two to three weeks is standard for a pentest RFP response period. Shorter timelines may exclude qualified companies. Allow additional time if your scope is complex or involves multiple environments.
Can I reuse a pentest RFP template for future engagements?
Yes. Build a reusable template with your standard evaluation criteria, compliance requirements, and communication expectations. Update the scope section for each new engagement. This reduces drafting time and keeps your process consistent.