6 Red Flags When Hiring a Penetration Testing Firm
Six warning signs that separate credible penetration testing firms from the ones cutting corners — covering methodology, reporting, scoping, insurance, and post-engagement support.
Not every penetration testing firm delivers the same quality of work. Some cut corners in ways that are hard to spot until the engagement is already underway - or worse, already over. This list covers six warning signs to watch for when evaluating pentest companies. Each one includes specific questions you can ask or things you can verify before signing a contract. Whether you are narrowing down a shortlist or comparing proposals, these red flags apply across company sizes and engagement types.
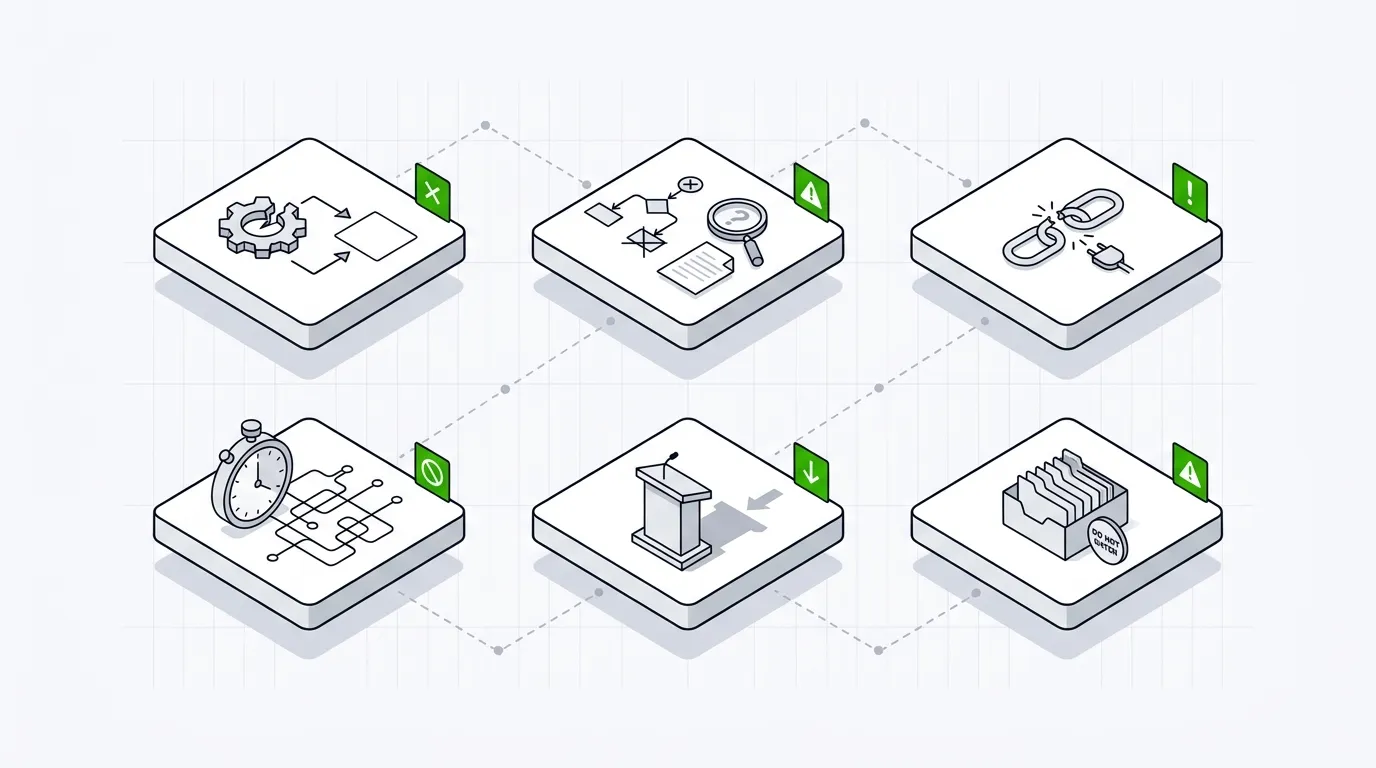
1. Automated-only testing sold as manual
Some firms run automated scanners and present the output as a manual penetration test.
A genuine manual pentest involves a skilled tester making decisions, chaining findings, and testing business logic - things scanners cannot do. If a firm’s proposal does not mention the testers involved, estimated manual hours, or the tools used alongside manual techniques, ask directly. Request a breakdown of how many hours are allocated to manual testing versus automated scanning. A firm that cannot clearly separate the two is likely relying too heavily on the latter.
2. No sample report available
A firm that will not share a redacted sample report may be hiding poor deliverable quality.
The report is the primary deliverable of any penetration test. You need to evaluate its structure, depth, and clarity before committing. Ask for a redacted or anonymized sample. Look for clear finding descriptions, evidence (screenshots, request/response pairs), severity ratings tied to a recognized framework, and actionable remediation guidance. If a firm refuses to share any example of their output, treat that as a serious concern.
3. Unclear or missing methodology
A credible firm can explain exactly how they will test your environment.
Ask what methodology the firm follows. Answers should reference recognized frameworks like OWASP Testing Guide, PTES, or OSSTMM - or a clearly documented internal methodology. Vague answers like “we use industry best practices” without specifics suggest the firm lacks a repeatable, structured approach. A well-defined methodology also helps you compare proposals on equal footing and ensures nothing important is left out of scope.
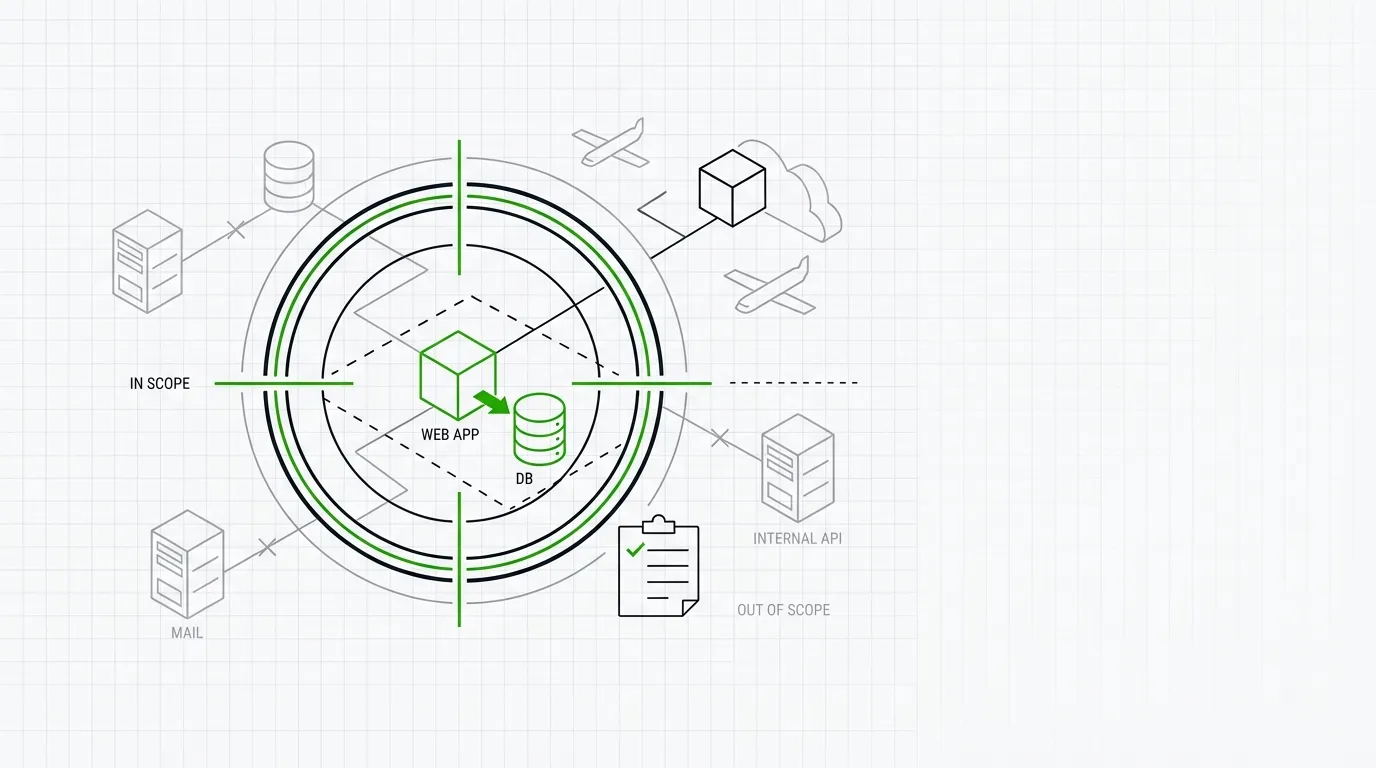
4. Vague scoping and pricing
If the scope is not clearly defined before work begins, the engagement will likely disappoint.
A thorough scoping process should cover target IP ranges, application URLs, user roles, testing windows, and any excluded systems. If a firm quotes a flat fee without asking detailed questions about your environment, the engagement is probably underscoped. Underscoped tests miss critical assets. Overscoped tests waste budget. Either way, you get less value. Push for a written scope document that both parties agree on before testing starts.
5. No professional indemnity or liability insurance
Testing without insurance puts your organization at unnecessary risk.
Penetration testing involves deliberate attempts to break into systems. Things can go wrong - data loss, service disruption, or unintended access. A firm should carry professional indemnity insurance and be willing to share proof of coverage. Ask for a certificate of insurance before signing. If a firm cannot or will not provide one, consider the risk you are accepting if something goes wrong during the engagement.
6. No remediation support after delivery
A report without follow-up support leaves your team to interpret findings alone.
The value of a pentest extends beyond the report. Your team will have questions about findings, need help prioritizing fixes, or want to verify that remediations are effective. Ask whether the firm offers post-engagement support - such as a debrief call, a Q&A window, or retest options. Firms that deliver a PDF and move on leave gaps in the remediation process. Even a short window of post-delivery support makes a meaningful difference.
These six red flags are straightforward to check during any procurement process. Ask direct questions. Request documentation. Compare what firms claim against what they can demonstrate. If you are building a shortlist of penetration testing companies, you can search pentest.fyi by location, services, certifications, and company size to find firms that match your requirements. From there, use these red flags to separate credible providers from the rest.
Frequently Asked Questions (FAQ)
How can I tell if a pentest firm is using only automated tools?
Ask for a breakdown of manual versus automated testing hours in their proposal. Request details on which testers will be assigned and what manual techniques they will use. If the firm cannot provide this, the engagement likely relies on scanners.
What should a good pentest report include?
A good report includes an executive summary, detailed technical findings with evidence, severity ratings based on a recognized framework (such as CVSS), and specific remediation steps for each finding. Ask for a redacted sample before you engage.
Is professional indemnity insurance standard for pentest firms?
Reputable firms carry professional indemnity insurance. It is not universal, especially among smaller or newer companies. Always ask for a certificate of insurance before work begins.
How detailed should scoping be before a pentest starts?
Scoping should cover all target systems, IP ranges, applications, user roles, testing windows, and any exclusions. Both parties should sign off on a written scope document before testing begins.
Can I use pentest.fyi to find firms with specific certifications?
Yes. pentest.fyi lets you filter companies by certifications such as CREST, CHECK, OSCP, and others, along with location, services, and company size. It lists 7,759 companies across 104 locations.